As Cisco was suggesting, the Firepower User Agent for Active Directory as an identity source for FMC was going to be removed in the future releases. In fact, as of FMC version 6.6.0 the Firepower User Agent is gone. The only option left is integrating FMC with ISE using pxGrid. I had intensively covered the pxGrid integration in this previous post.
However, in this post I want to show you how to configure the Firepower User Agent on FMC. Configuring the User Agent is a very simple operation. But that would not be enough to allow us to use the user contexts in FMC. We still need to configure a realm and and identity policy. I covered both these topics in previous posts. Check out more about the realm configuration in this post, and identity policy in this one.
There are two parts to configure the Firepower User Agent. One is on the Windows server side and another on the FMC. In this lab we will start configuring the User Agent on FMC, and then will move to the Windows server. You can download the User Agent from Cisco website at this link.
The User Agent configuration on the FMC is really a very simple task, same for the installation on the Windows. The installation of the User Agent does not necessarily has to be on the Active Directory. It can be done on any Windows machine on your network, as long as that machine can talk to the AD. The reason why this is possible is because within the User Agent configuration we provide the AD admin account and password. That is, through those credentials, the User Agent can connect to the AD from any machine on the network that have a L3 adjacency with the AD.
We will start with the FMC configuration and then we will move on to the Windows Active Directory. The FMC version we are using in this lab is version 6.5.0.4. And the Firepower User Agent is the latest which is version 2.5-147.
Step 1: Configure Firepower User Agent Identity Source on the FMC
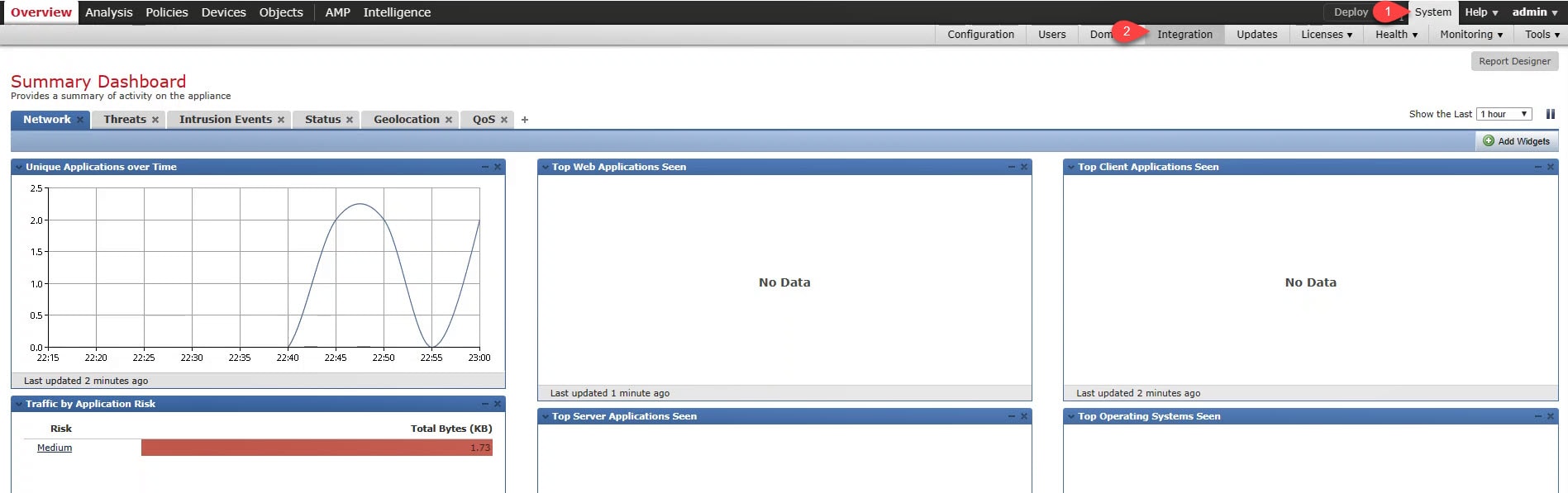
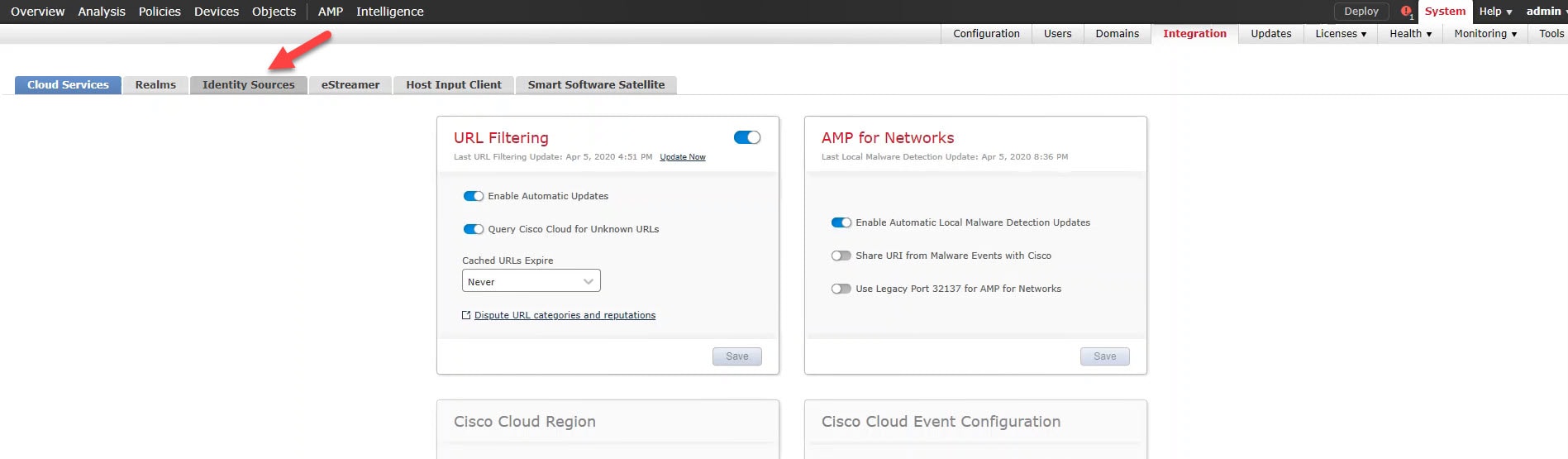
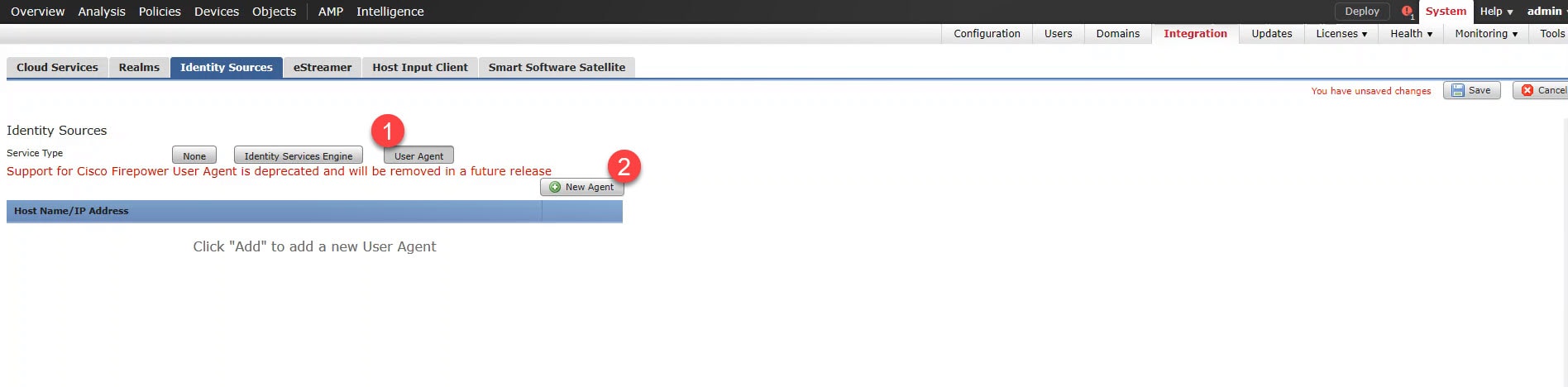
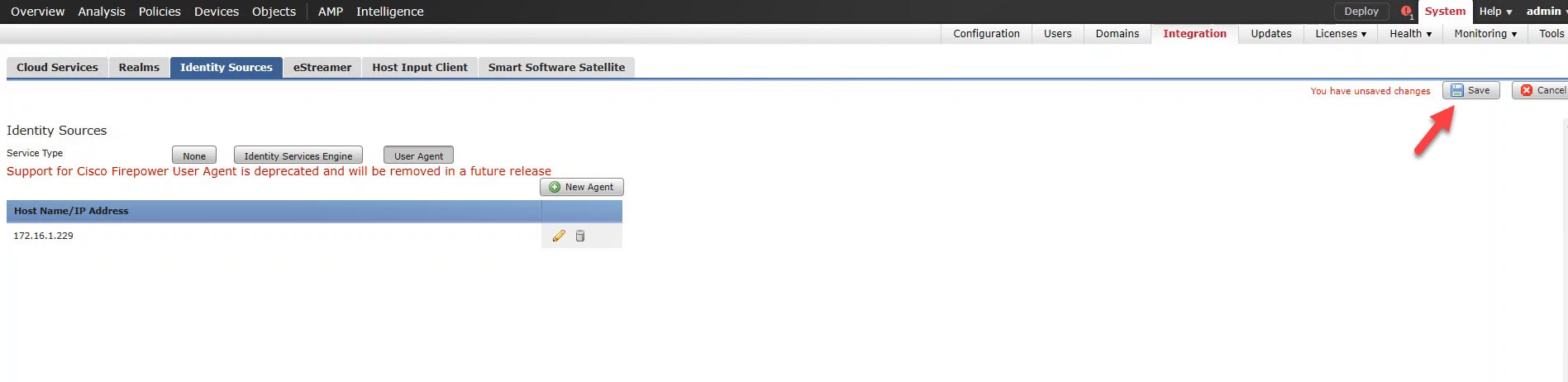
Go to System > Integration > Identity Sources > User Agent > New Agent
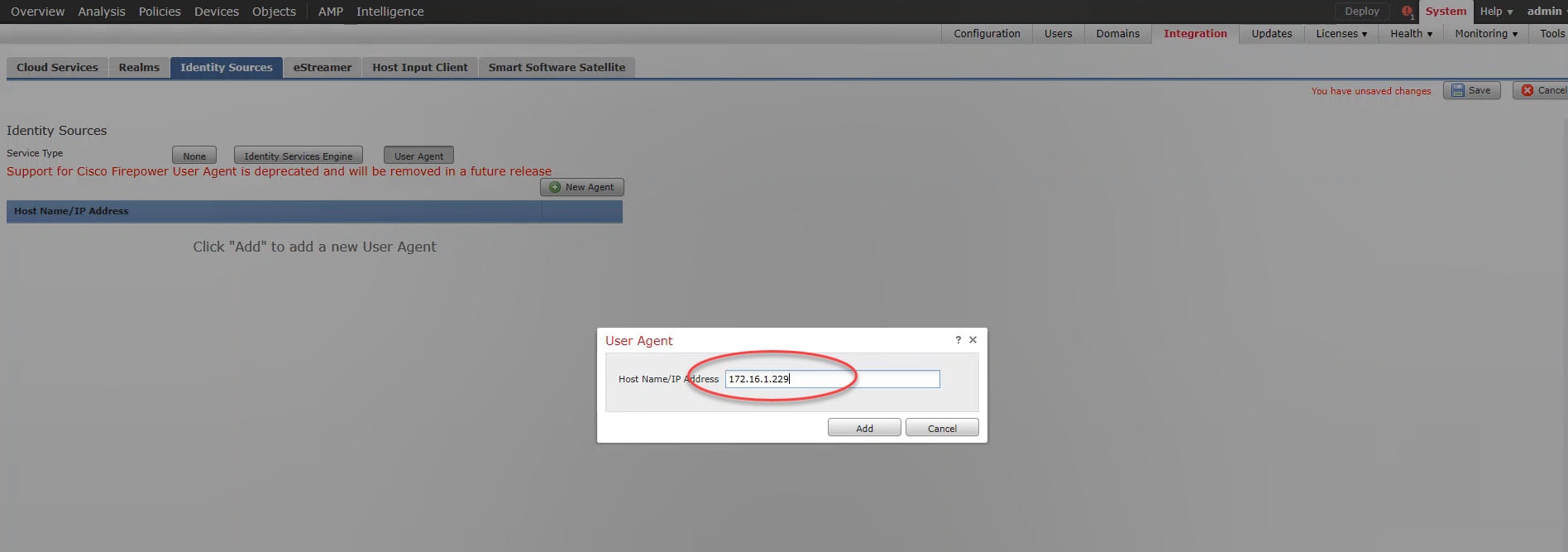
Type the Active Directory (or the Windows machine) IP address where the User Agent will be installed, click Add, and finally click Save
Step 2: Configure Firepower User Agent authentication password on the FMC CLI
Go to the FMC CLI and use the following command to set the Firepower User Agent authentication password
This step is optional and it was added in Firepower User Agent version 2.5. Let's use it just for fun.
> configure user-agent Enter new password for user-agent: Confirm new password for user-agent: Password was successfully updated. >
The password must contain a number, a special character, both upper and lower case characters, and must be at least 8 characters long.
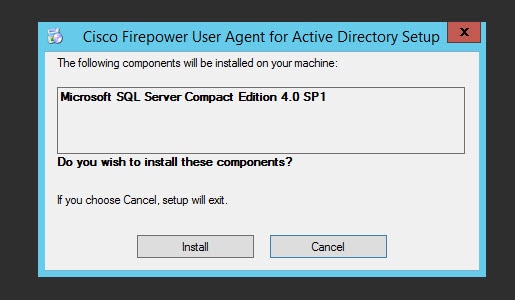
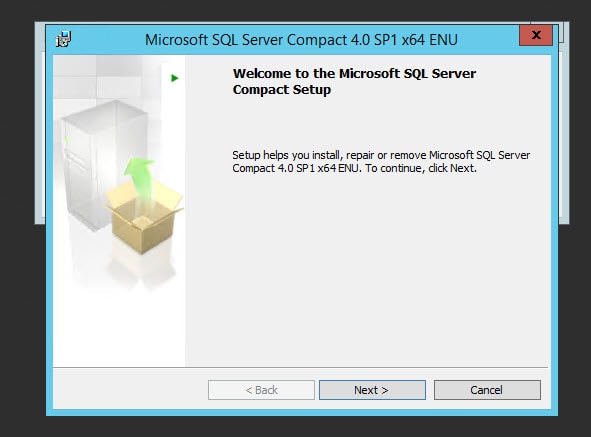
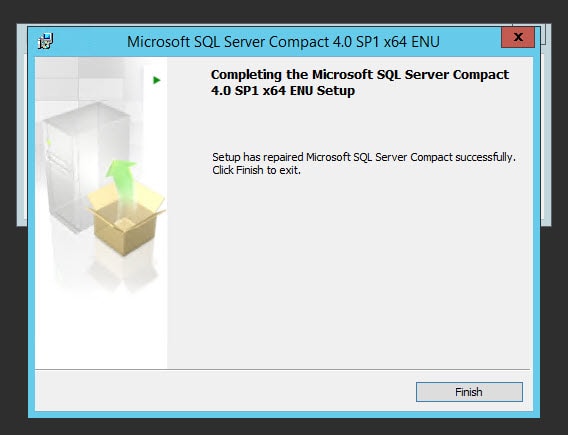
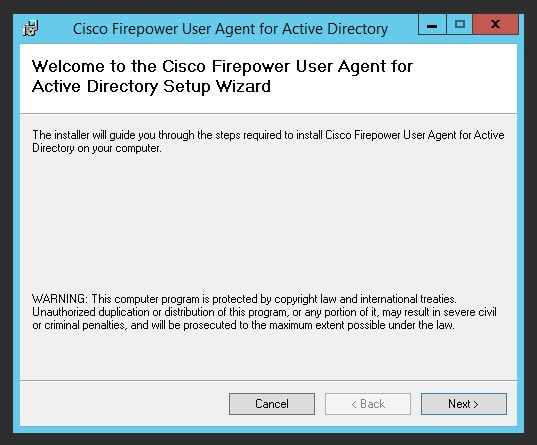
Step 3: Install Firepower User Agent on the Active Directory
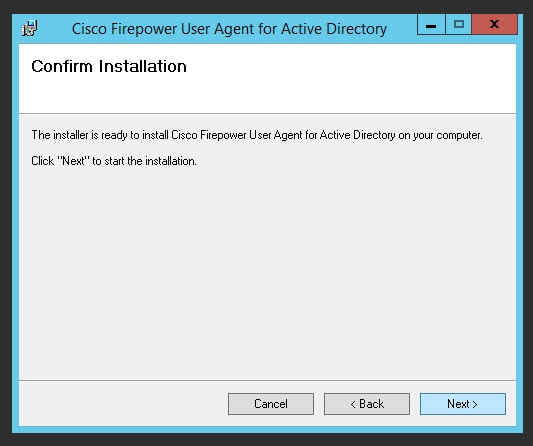
Step 4: Configure Firepower User Agent on the Active Directory
Give the User Agent a name, ensure the service is running, if not click on the play icon, and save
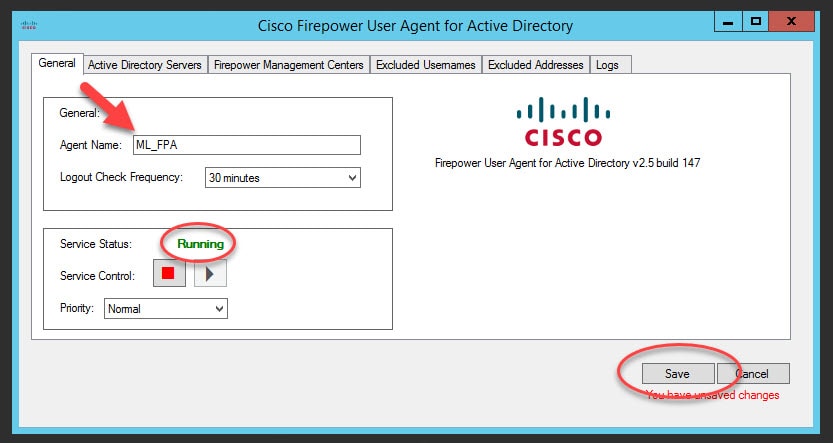
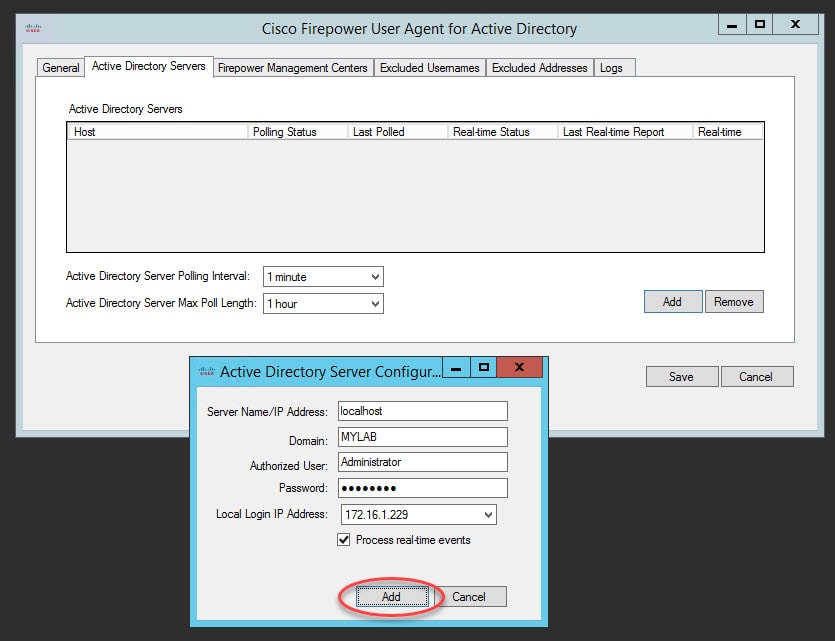
Go to Active Directory Servers tab, click on Add, fill up the Active Directory details and click on Add
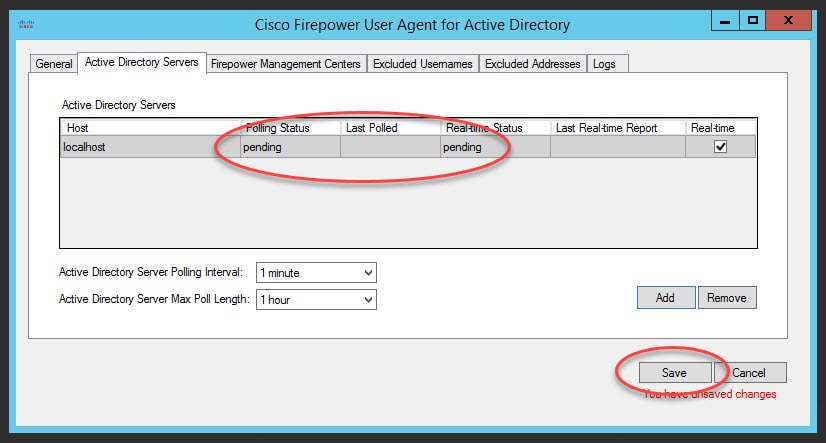
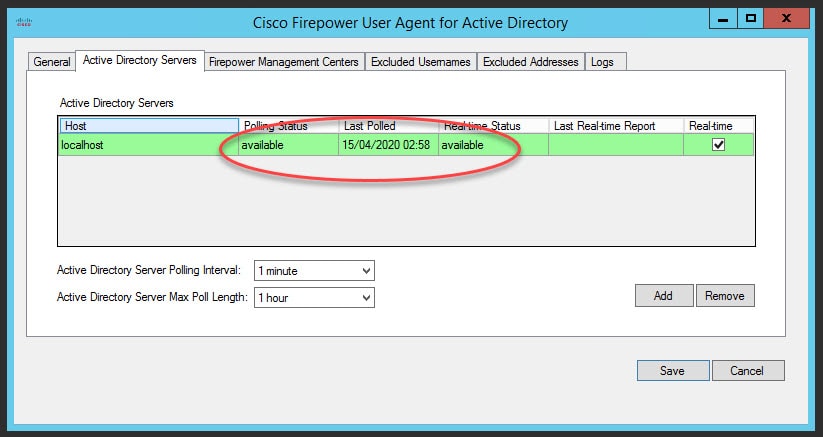
The polling and real-time status will show as pending. However, once you save it should change to available.
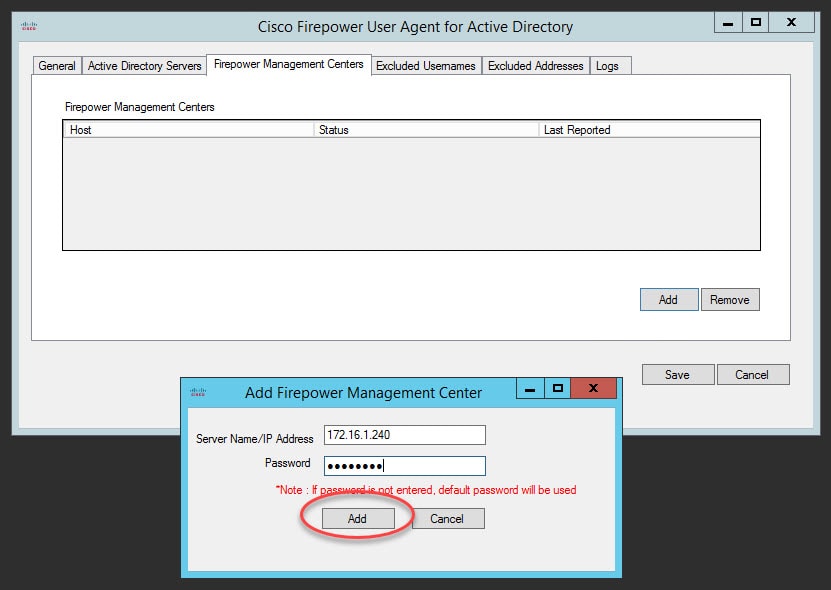
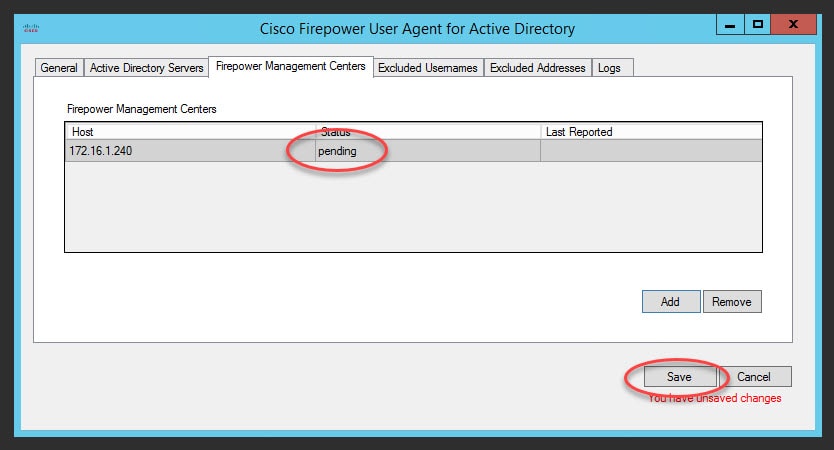
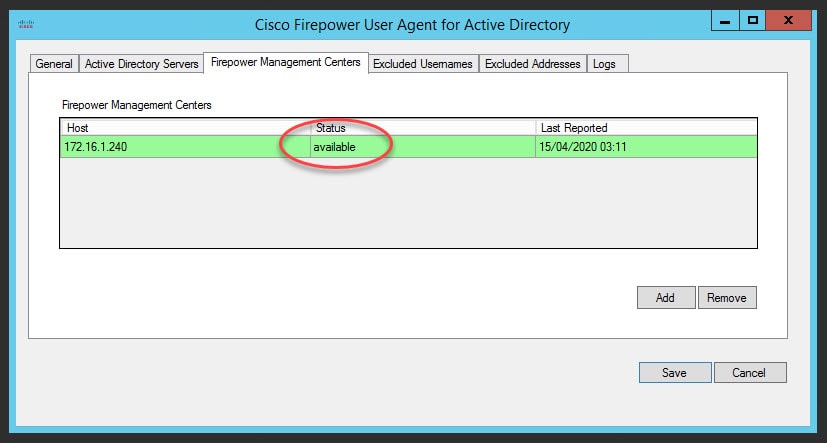
Go to Firepower Management Centers tab and click on Add, type the FMC IP address and the password you sat in step 2
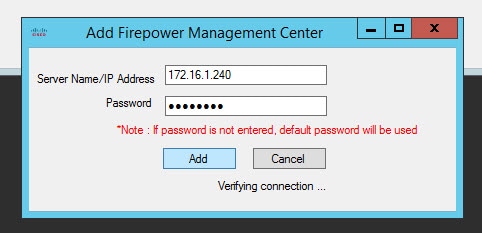
The Firepower User Agent will try to authenticate to the FMC MySQL database with the password you typed. If the connection is successful it will go in pending status. Once you save it should change to available.
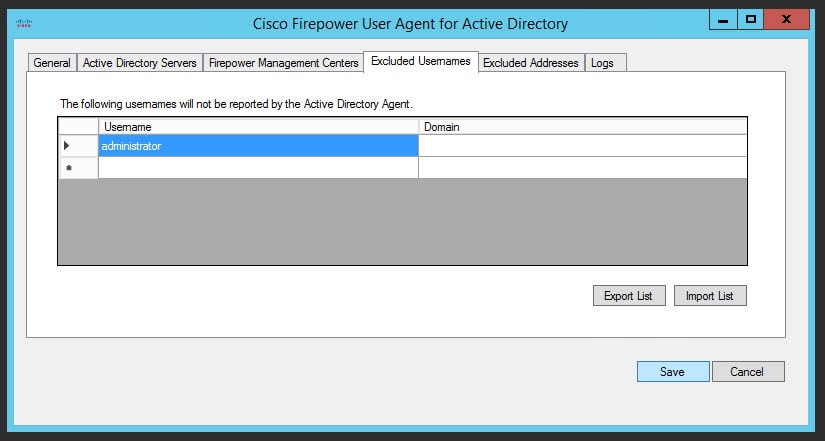
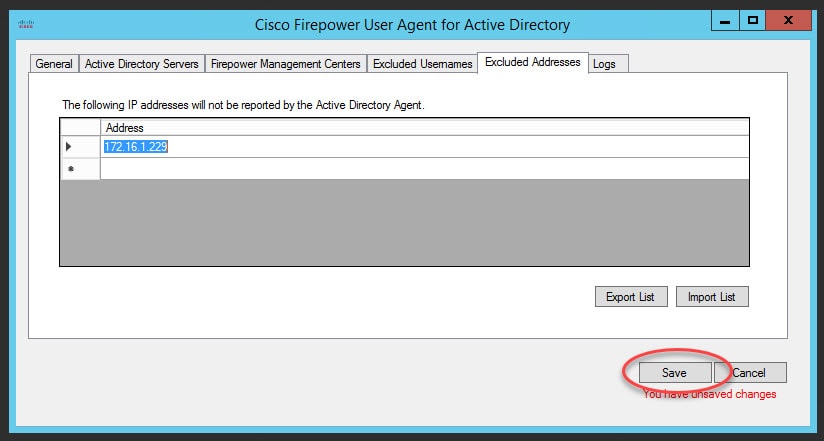
The Excluded Usernames and Excluded Addresses tabs are dedicated to define any username or IP address values that you don't want the Firepower User Agent to share with the FMC. Typically you would define the admin usernames, service accounts and the servers IP addresses. In other words these details would be suppressed from being monitored by the Firepower User Agent. Accordingly, the FMC will not receive any data regarding them.
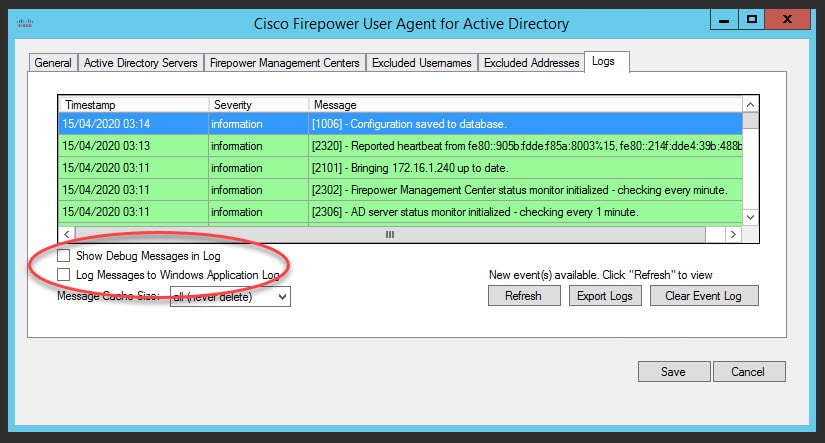
The Logs tab it to check the Firepower User Agent logs. However, there are a couple of useful options that you can enable. The Show Debug Messages in Log option will give you some useful verbose logs to help you troubleshooting issues related to the Firepower User Agent and the communication with the FMC.
When you enable the Show Debug Messages in Log option, you will see an additional tabcalled Maintenance. This additional tab allows you to clear the Firepower User Agent cached data. Also, that tab allows to raise the debug logging level. The Log Messages to Windows Application Log option will redirect the Firepower User Agent logs to the Windows Events.
Lastly, here is how the Firepower User Agent was totally removed from the FMC starting from version 6.6.0.
This wraps up this post about Cisco Firepower User Agent.
Thank you for reading!


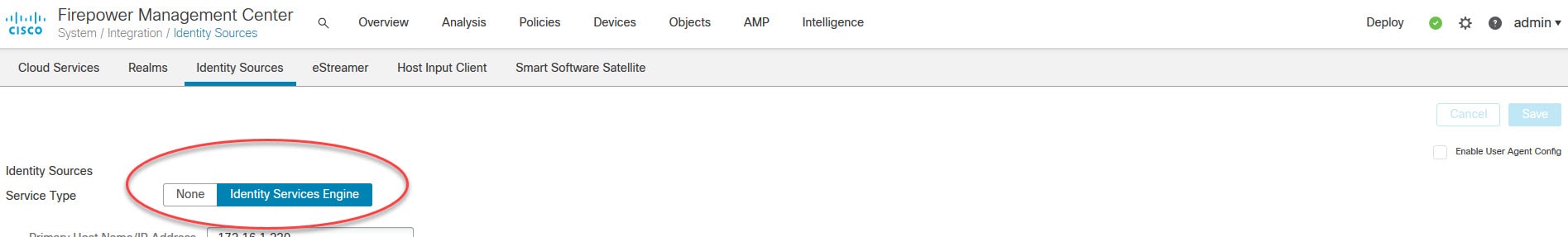
Your article is inaccurate, user agent hasn’t been removed from 6.6, you have to enable the check box and it then says it’s deprecated.
You are right indeed, I’ve done a 6.6.1 Firepower deployment recently, and I had enabled the user agent as you mentioned. I might be wrong, but I fairly remember that there was no option on the 6.6.0 to enable it, however, on the 6.6.1 that option is there.